Security Assessment
At DigiClouds, our SecOps-driven Cyber Security Assessment equips organizations with proactive defense strategies through automation, continuous monitoring, and rapid incident response. By integrating IT operations with advanced cybersecurity practices, we enhance your cloud security posture and ensure compliance with regulatory standards. Our team delivers end-to-end threat detection, risk assessment, and real-time security management—helping prevent breaches before they occur.
Threat Detection & Monitoring
- Real-time visibility into cloud workloads, identities, and traffic patterns.
- Integrated with cloud-native services and third-party SIEM platforms.
-
Monitoring Tools Used:
- Amazon GuardDuty, AWS CloudTrail
- Azure Defender, Microsoft Sentinel
- GCP Security Command Center
- Detection rules for anomalies, malware signatures, and suspicious behavior.
Identity & Access Management
- Evaluation of role-based access controls, permission boundaries, and identity lifecycle.
- Enforcement of Zero Trust principles and least privilege access.
-
IAM Components Reviewed:
- AWS IAM Policies
- Multi-Factor Authentication (MFA)
- SSO & Identity Federation Integrations
- Detection of over-permissioned accounts, inactive credentials, and exposed secrets.
Compliance Auditing
- Deep inspection of cloud configurations to ensure adherence to best practices and industry standards.
- Automated scans against benchmarks (e.g., CIS, NIST, ISO 27001).
-
Compliance Tools Used:
- AWS Config, Azure Policy, GCP Security Health Analytics
- Prisma Cloud, Tenable.io, Qualys Cloud Security
- Compliance reports for HIPAA, GDPR, PCI-DSS
- Recommendations generated with severity tags and remediation steps.
Core Features
Our Cyber Security Assessment services provide a comprehensive evaluation of your cloud and on-premises infrastructure. We identify vulnerabilities, test existing defenses, and validate compliance with industry standards—ensuring a proactive, secure, and resilient IT environment.
Application Security
We assess web and mobile applications to uncover vulnerabilities such as injection attacks, insecure authentication, and misconfigurations—applying OWASP-based testing methodologies to ensure robust security.
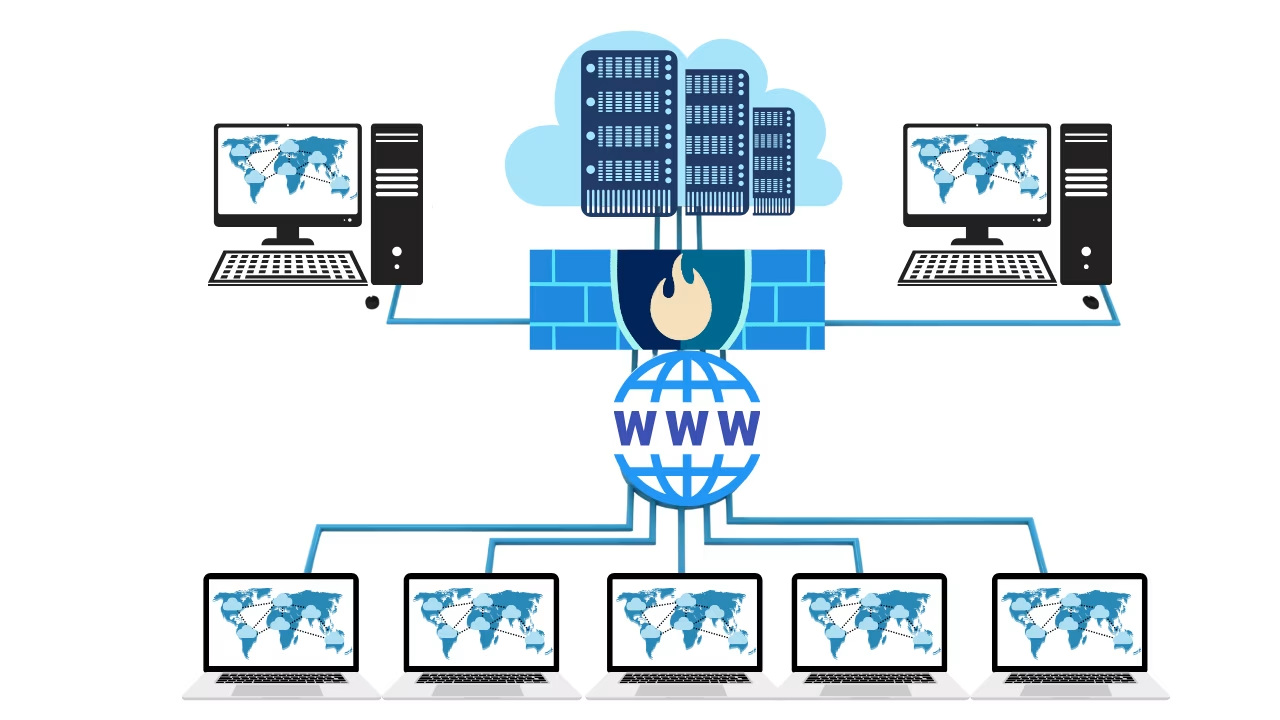
Wireless Network Security
We evaluate Wi-Fi networks for weak encryption, unauthorized access points, and insufficient segmentation—mitigating risks of exploitation, data leaks, and unauthorized access.
Penetration Testing
Simulate real-world cyberattacks on your infrastructure to identify and remediate exploitable vulnerabilities—strengthening your defenses before malicious actors can take advantage.
Red Team Assessment
Execute full-scale attack simulations to assess your organization’s ability to detect, respond to, and contain advanced persistent threats (APTs) and insider risks—providing actionable insights to strengthen your security posture.
Testing Capabilities
At DigiClouds, our Cybersecurity Assessment framework covers a broad spectrum of testing methodologies designed to identify vulnerabilities, validate controls, and improve your overall security posture. We go beyond surface-level scans to deliver actionable insights through advanced assessments across cloud, network, endpoint, and application layers.
Pen Testing
Simulate real-world attacks to expose exploitable system flaws and security gaps.
Cloud Audit
Review cloud permissions, configs, and services for misconfigurations and compliance risks.
Access Review
Detect privilege escalation, inactive accounts, and excessive permissions across systems.
Endpoint Check
Assess patch status, malware defenses, and encryption across devices and servers.
App Security
Scan for OWASP vulnerabilities in your websites, APIs, and business apps.
Phishing Tests
Run social engineering and email attack simulations to test employee awareness.
Why Choose DCS ?
Defined Assessment Scope
We clearly define the systems, networks, and compliance areas included in the assessment—ensuring a focused, efficient, and goal-oriented security evaluation.

Comprehensive Risk Analysis
We identify threats and vulnerabilities, evaluate their potential business impact, and prioritize risks—enabling you to make informed decisions and strengthen your overall security posture.

Policy & Procedure Review
We evaluate your existing security policies and procedures to ensure alignment with industry best practices, regulatory requirements, and internal governance controls—fostering a strong, compliant, and resilient security framework.

Deep Technical Assessment
We perform thorough vulnerability scanning, penetration testing, and endpoint audits to identify exploitable security gaps—providing comprehensive visibility across your digital assets.

Result Analysis & Reporting
Following the assessment, we provide detailed reports outlining prioritized risks, technical findings, and actionable remediation recommendations—empowering your team to address vulnerabilities effectively.

Actionable Security Guidance
Our experts deliver tailored, practical strategies to enhance your security posture—boosting resilience and ensuring alignment with your compliance objectives.
Certified
Our cybersecurity specialists hold globally recognized certifications across AWS, Azure, and Google Cloud, ensuring expert implementation of secure architectures, compliance-focused controls, and proactive threat mitigation strategies.

AWS Security
Certified in AWS Security Specialty, our experts implement robust identity and access controls, encryption, continuous monitoring, and advanced threat detection using services such as IAM, CloudTrail, and GuardDuty.

Azure Security
Microsoft Certified in Security, Compliance, and Identity, our specialists manage Azure Defender for Cloud, Azure Active Directory, Conditional Access, and policy enforcement to maintain secure and compliant cloud environments.

Google Cloud Security
Certified in Google Professional Cloud Security, our team ensures secure configurations, IAM policy design, threat intelligence integration, and workload protection using native GCP tools and best practices.

Easy to use Control Panel
Simple and effortless management — our web hosting plans come with an easy-to-use control panel that lets you manage your website, emails, databases, and more with ease.